02. Hacking
Botnet Resources
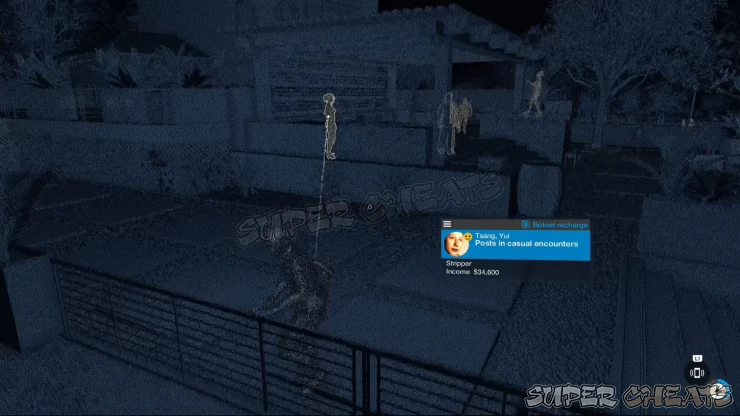
This is represented by the circular gauge in the lower right corner of your screen. Certain hacking abilities like controlling vehicles, city disruptions, or vehicle takedowns consume botnet resources. They regenerate over time; however, you can also hack civilians with the lightning bolt icon to drain their Botnet resources. You can also increase your botnet capacity by spending Research Points in the ./Research App.

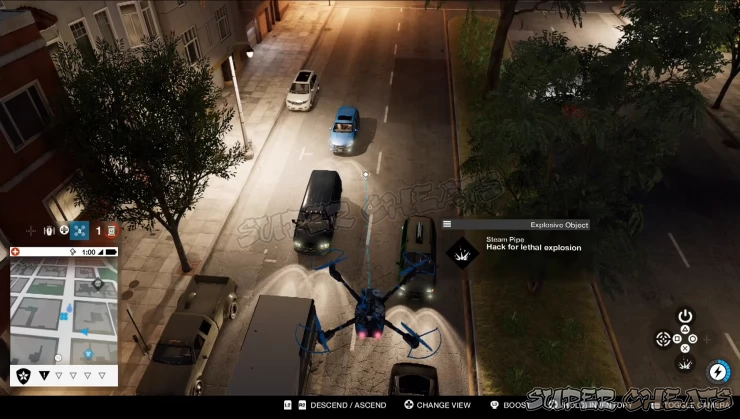
Hacking: Objects
When a hackable object is within range, press and hold L1 to open the hacking module and press the corresponding button to trigger the desired effect.
- Press X to trigger the object’s function (detonate or stun)
- Press Square to activate a proximity trigger.
- Press Triangle to shutdown the object for a set amount of time.
- Press Circle to attract nearby people towards the object. Perfect for luring them towards the activated proximity traps you set earlier.
Hacking: People
When targeting a person, press and hold L1 button to open the hacking module and press the corresponding button to get the desired action. The available options may vary when you’re targeting a civilian or hostile.
- Press X - Acquire different rewards like intel (voice or chat), Botnet Resources. If you’re targeting hostiles carrying explosives, you can sometimes detonate them remotely by pressing this button. For other civilians, you can overload their phones to trigger a non-lethal shock.
- Press Square - Call the police on the target(requires upgrade)
- Press Triangle - to distract the target. This will also prevent their outgoing calls from going through, great for stopping enemies for calling reinforcements or witnesses calling 911.
- Press Circle - To call a gang on the target. (requires upgrade)

Hacking: Vehicles
While targeting a vehicle, hold L1 to open the hacking module and press the corresponding button to get the desired action. You can perform these actions on occupied or parked vehicles and it costs botnet resources. Hacking vehicles is a good way to stop fleeing enemies on their tracks or forcing them to crash. You can also use this to remove the cover of enemies hiding behind them, run over someone, or even use them as car bombs by strapping explosive devices on them and turning on the proximity.
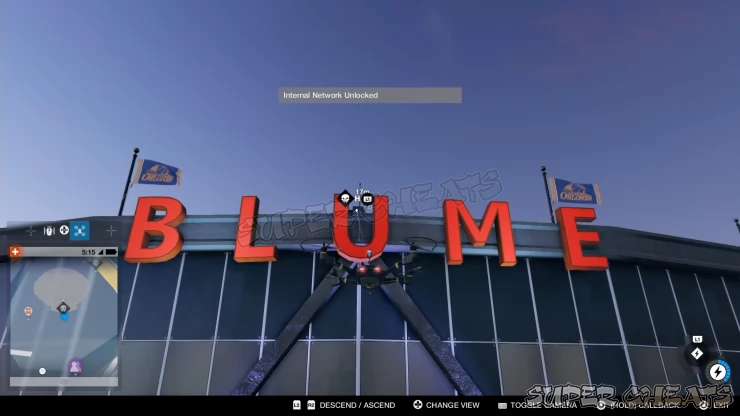
Lock: Access Key
Some doors need an access key to unlock. Use the NetHack vision to reveal the access key source. Press L1 to hack the access key and to unlock the door. You can conveniently get the access key using your drones.
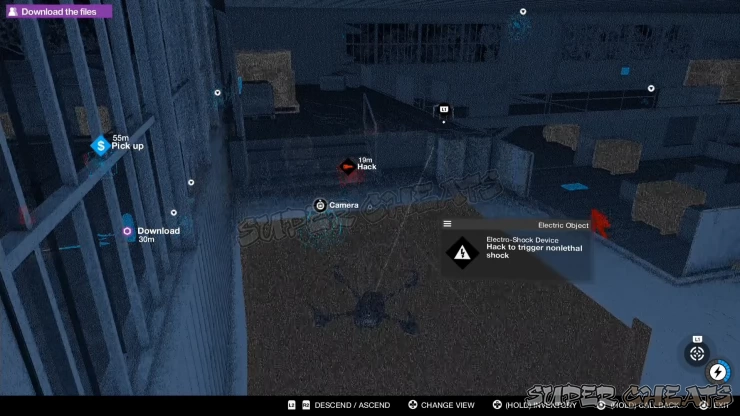
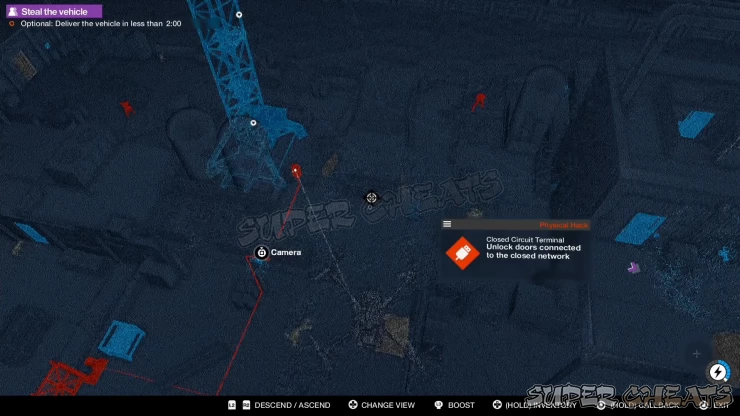
Lock: Closed Circuit Terminal
There are important access points, usually containing Research Points and Key Data that are locked by Closed Circuit Terminals. While the access points can be hacked remotely, CCTs require to be physically hacked, either by Marcus or using your trusty Jumper. If an access point is locked, use NetHack to follow the data flow from the access point to the CCT. Once done, you can continue scouting the area for any good entry points for yourself or for your drone to enter.

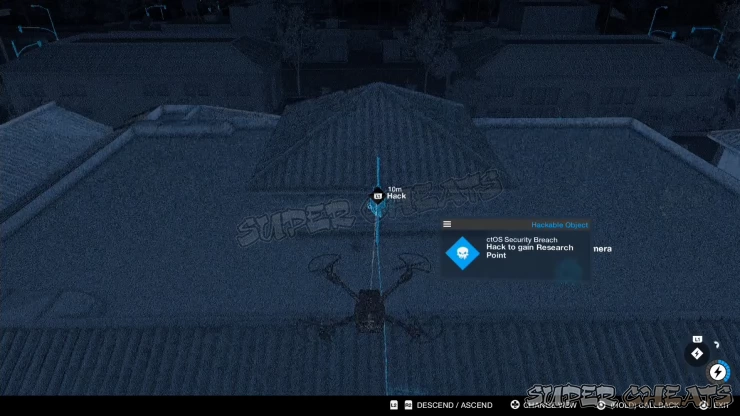
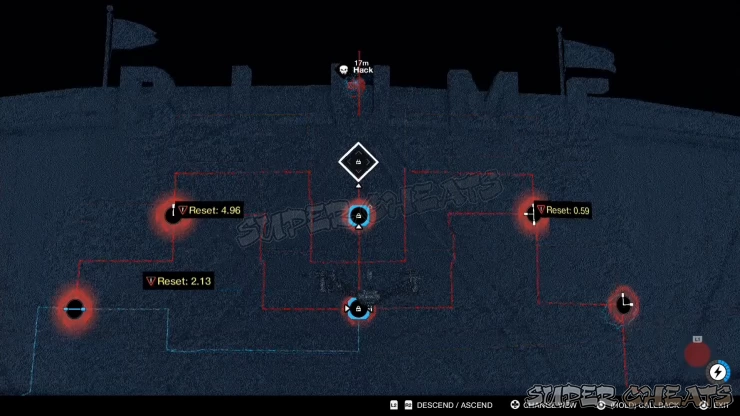
Lock: Network Bypasses
Some access points are protected by even more complex network bypasses. These are similar to a puzzle mini-game since you have to rotate and unlock the nodes to complete the data flow. First step for solving network bypasses is by finding the data source. These are usually hidden or out of reach that you can only activate them by using your drones or within the view of nearby cameras. Once activated, use NetHack to follow the trace of the data flow and locate where the flow is interrupted.

There are certain locked nodes that may require at least two connections flowing to it so you have to make sure that the data flow is flowing properly for that node. There are also nodes that reset after a set amount of time so you have to complete the bypass before the timer run out. After linking the data flow towards the last node, hack it to complete the bypass.
Mass Hacks
Once you have researched the necessary skills for Mass Hacks, they’ll be available in your Equipment Wheel. You can equip them by holding the up button in your DPAD then press R1 to use the equipped mass hack. Mass Hacks recharge over time.
- Mass Comms Disruptor - Simultaneously create a distraction on everyone around you.
- Mass Systems Crash -Shuts down all city infrastructure for 30 seconds. This can be upgraded to Blackout which will turn off all lights in the area, reducing line-of-sight on top of shutting down all infrastructure within range.
- Mass Vehicle Hack - When on foot, create mayhem by hacking all cars in the area at once. While driving, hack vehicles to distract drivers and clear a path which lasts for 10 seconds.
NetHack
NetHack is a helpful vision which will enable you to locate hackable objects, collectible, intel, hostiles, and more. This vision gives you a good view of things not visible in the naked eye like data flow connections or consoles. This also highlights the gates, vents, hatches, and other entrances that you can remotely open or close. You can toggle this view by pressing the right stick.
- Blue Objects: Key Data, Rewards, hackable objects, cameras, and RC devices.
- Red Objects: Locked objects and enemies
- Orange Objects: Objectives and intel.
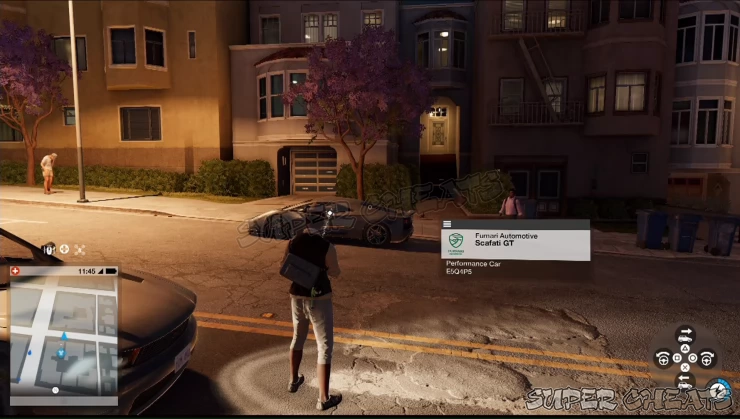
Profiling
Use the profiler to get more information about people and objects. Whenever you’re near an object or civilian, your phone will automatically target the nearby persons, objects, and vehicles. Pressing L1 will bring up the hacking module and more information about them. For people, you’ll see some of their personal info and what kind of action you can do with them. For vehicles, you can see their model and manufacturer. For hackable objects, you’ll see whether they can be set for lethal or non-lethal explosions, if they need physical hacking, etc. When remotely accessing a camera or using NetHack, profiling is automatic.
Quick Hack
While targeting an object, person, or vehicle, you’ll see an icon near the Botnet Module in the lower right corner of your screen. Press L1 will trigger the icon shown there without the need of bringing up the hacking module.

Remote Control
There are devices that can be remotely controlled like scissor lifts, forklifts, and cranes that can help you reach out-of-reach and elevated places. You can remotely control them using nearby cameras or relayed by your drones. When you see an RC object, press and hold the square button to take control of it completely. Scissor lifts and forklifts can be moved similar to vehicle controls and their lifts can be lowered or raised as well. If you just want to remotely control them, press and hold the L1 button to open their control options and use the designated buttons to make them perform basic movements.

Security Cameras
Press and hold the square button to take control of the targeted security camera. While controlling a security camera, you’ll be able to spot and tag hostiles and even take photos. When NetHack is activated, you can see other nearby cameras behind walls and jump to them instead. This gives you a good look inside a restricted compound without the risk of alerting guards. While in control of a camera, you can still perform normal hacking functions like remotely setting off junction boxes, take control of RC objects, set proximity triggers, obtain access keys, and use the profiler function.

Security Systems
There are two types of security systems: motion detectors and security lasers. When triggered, this will automatically alert all the security guards in the area you’re trying to break in. You can use NetHack to reveal a motion detector’s scanning point or trigger. Press L1 + triangle to shut down the security system to pass by undetected.

Anything missing from this guide?
ASK A QUESTION for Watch Dogs 2
Comments for 02. Hacking
Add a comment
Please log in above or sign up for free to post comments- Basics
- Main Operations
- Side Operations
- ./Research App Upgrades
- Key Data Locations
- Scout X Locations
- Other Collectibles
- Online Operations
- Activities: Drive SF
- Trophies
 Join us on Discord
Join us on Discord
